Dns Server Configuration In Rhel6 Step By Step Pdf
How to configure dns server in rhel 7 step by step. dns server configuration in linux step by step centos. Bind chroot. dns server configuration in linux step by step centos. How to configure dns server in rhel 7 step by step.
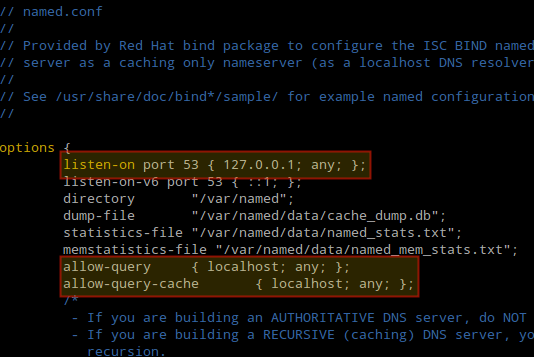
Named chroot. Bind allow query. Install bind centos 7. Configure forward zone file and reverse zone file using named chroot using centos or rhel 7. Sample forward zone file and reverse zone file on rhel 7 linux.
This configuration: ○ The policy source (the standalone or primary Policy Broker and its Policy Server) resides on the TRITON management server machine. □ This configuration is. Step 9: (Web DLP module only) Install Linking Service on the management server, page 25. Secondary DNS server for network interface C.

Dns Server Configuration In Rhel 6 Step By Step Pdf C++
Verify bind dns server configuration files using named-checkconf. Do not copy chroot contents to /var/named/chroot. Dns configuration step by step. Setup dns server on red hat.Install Bind Chroot RPMTo install BIND running in a chroot environment, you have to install the bind-chroot package.
If you do not have an active repository then using which then. root@node3 # yum install -y bind-chrootVerify the list of available bind packages installed with bind chroot via yum: root@node3 # rpm -qa grep bindbind-license-9.9.4-74.el76.1.noarchbind-chroot-9.9.4-74.el76.1.x8664keybinder3-0.3.0-1.el7.x8664bind-libs-9.9.4-74.el76.1.x8664bind-utils-9.9.4-74.el76.1.x8664bind-libs-lite-9.9.4-74.el76.1.x8664bind-9.9.4-74.el76.1.x8664rpcbind-0.2.0-47.el7.x8664Below list of directories and files will be created with bind chroot package on your RHEL 7 Linux host. For the reverse zone, here since our IP is 10.0.2.32, I have used 2.0.10.in-addr.arpa as the zone name, similarly if your IP is 192.168.0.XX then your reverse zone name syntax would be 0.168.192.in-addr.arpaWe will create our forward and reverse zone files in the next steps.Create Forward Zone FileNavigate to /var/named where we will have some default templates which can be used to configure our forward zone file. root@node3 # cd /var/named/List the content of /var/named root@node3 named# ls -ltotal 32drwxr-x-. 2 root named 4096 Jun 21 16:12 chrootdrwxrwx-.
2 named named 4096 Jun 5 00:56 datadrwxrwx-. 2 named named 4096 Jun 5 00:56 dynamic-rw-r-.
Rhel 6 Release
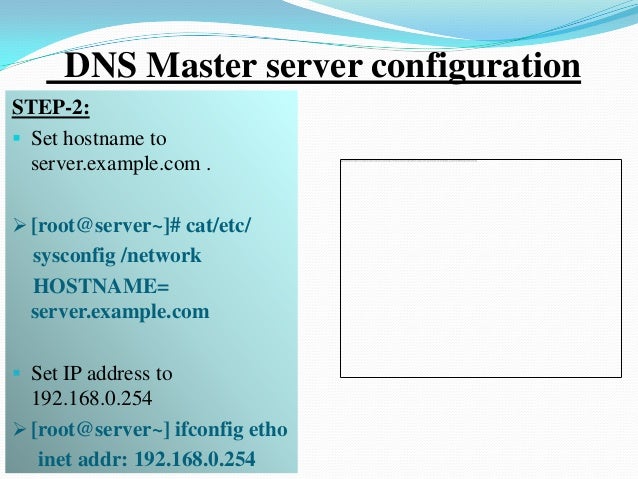
1 root named 2281 May 22 2017 named.ca-rw-r-. 1 root named 152 Dec 15 2009 named.empty-rw-r-. 1 root named 152 Jun 21 2007 named.localhost-rw-r-. 1 root named 168 Dec 15 2009 named.loopbackdrwxrwx-. 2 named named 4096 Jun 5 00:56 slavesCreate forward zone file using named.localhost root@node3 named# cat named.loopback example.com.zoneChange the permission and ownership of the forward zone file ( example.com.zone) as shown below: root@node3 named# chmod 644 example.com.zoneroot@node3 named# chown root:named example.com.zoneroot@node3 named# ls -l example.com.zone-rw-r-r-.
1 root named 260 Jun 21 16:28 example.com.zoneUpdate the forward zone file with the details from your setup and environment. Below is my sample forward zone file. root@node3 named# cat example.com.zone$TTL 1D@ IN SOA example.com root (1; serial1D; refresh1H; retry1W; expire3H ); minimumIN NS localhostlocalhost IN A 127.0.0.1node1 IN A 10.0.2.30node2 IN A 10.0.2.31node3 IN A 10.0.2.32Create Reverse Zone FileSimilarly create a reverse zone file using named.localhost. root@node3 named# cat named.localhost example.com.rzoneChange the permission and ownership of the reverse zone file ( example.com.rzone) as shown below: root@node3 named# chmod 644 example.com.rzoneroot@node3 named# chown root:named example.com.rzoneroot@node3 named# ls -l example.com.rzone-rw-r-r-. 1 root named 260 Jun 21 16:28 example.com.rzoneNext update the values of your reverse zone file depending upon your environment. Below is my sample reverse zone file: root@node3 named# cat example.com.rzone$TTL 1D@ IN SOA example.com.
(1; serial1D; refresh1H; retry1W; expire3H ); minimumIN NS localhost.30 IN PTR node1.example.com.31 IN PTR node2.example.com.32 IN PTR node3.example.com. root@node3 # cat /etc/resolv.conf# Generated by NetworkManagersearch example.comnameserver 10.0.2.32nameserver 8.8.8.8Verify Bind Chroot DNS ServerNow you can use different tools to verify your bind chroot DNS server configuration. In this example I am using nslookup and dig to verify my forward and reverse zone configuration root@node3 # nslookup node1.example.comServer: 10.0.2.32Address: 10.0.2.32#53Name: node1.example.comAddress: 10.0.2.30So the nslookup was able to get a response for node1.example.com using our bind chroot DNS server 10.0.2.32. Similarly look out for ANSWER SECTION using dig command for reverse zone file content. root@node3 # dig -x 10.0.2.30; DiG 9.9.4-RedHat-9.9.4-74.el76.1 -x 10.0.2.30;; global options: +cmd;; Got answer:;; -HEADER.